Linux Kernel Security Disclosure Protocol and CVE-2026-31431 Technical Analysis
The Linux kernel security team prioritizes immediate public commits over downstream coordination, creating a systemic "security lag" for major distributions. This policy ensures that fixes reach publi

The Pitch
The Linux kernel security team prioritizes immediate public commits over downstream coordination, creating a systemic "security lag" for major distributions. This policy ensures that fixes reach public trees quickly but leaves Ubuntu, RHEL, and Gentoo users exposed to public exploits for days before official patches arrive.
Under the Hood
The current friction stems from the kernel's refusal to provide exclusive early access to security fixes (Source: kernel.org). This philosophy was tested recently by CVE-2026-31431, nicknamed "Copy Fail," a CVSS 7.8 local privilege escalation flaw in the algif_aead module that has existed since 2017 (SentinelOne, Theori).
Theori discovered the vulnerability using "Xint Code," an AI-powered scanner, which identified the memory corruption primitive in approximately sixty minutes of scan time (Bugcrowd, Theori). While mainline maintainers committed a fix on April 1, 2026, they did not notify distribution maintainers through the standard 'linux-distros' mailing list (Openwall, Sam James).
By April 29, 2026, a 732-byte Python PoC exploit was published, providing a functional path for container escapes in shared-kernel environments (CERT-EU, Theori). At that time, several major distributions had not yet pushed official security updates to their stable channels (Help Net Security).
Production teams currently have two primary options for mitigation:
- Deploying a community-developed eBPF probe to block the exploitation primitive (Dabbleam/CVE-2026-31431-mitigation).
- Disabling the AF_ALG crypto subsystem entirely, assuming no local services rely on the user-space interface.
We don't know yet if the public outcry from maintainers like Sam James will force a restructure of the 'linux-distros' notification process. Additionally, while Hacker News threads suggest certain legal or governmental pressures influence this "no-notification" stance, those claims remain unverified (HN).
Marcus's Take
The Linux kernel security protocol is fundamentally mismatched with the speed of modern offensive AI tools. Expecting downstream maintainers to monitor every mainline commit for silent security fixes is a fantasy that creates a multi-day window for trivial container escapes. If you are running multi-tenant workloads on shared kernels, you cannot rely on your distribution's patch cycle alone; you must implement the eBPF mitigation or disable the algif_aead module immediately.
Ship clean code,
Marcus.

Marcus Webb - Senior Backend Analyst at UsedBy.ai
Related Articles
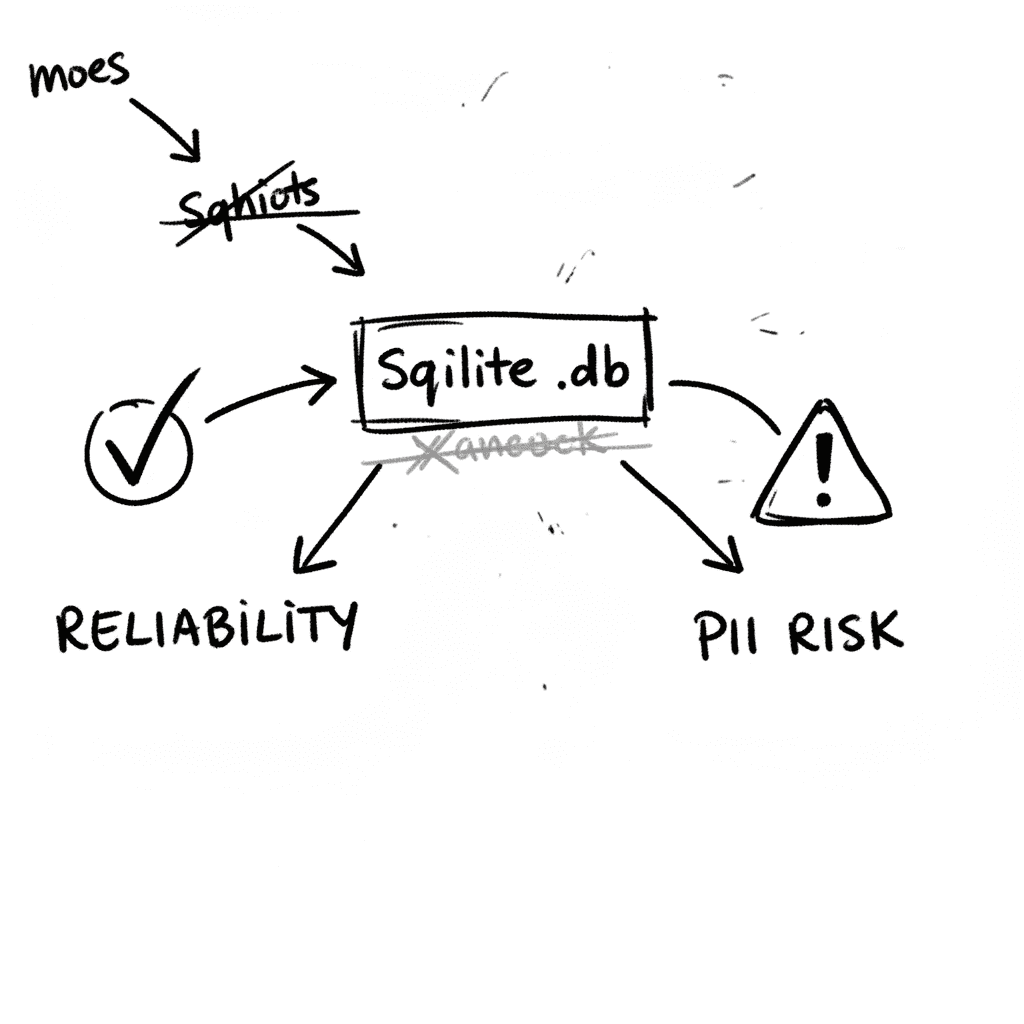
SQLite 3.53.1: Technical Reliability vs. Compliance Governance
SQLite is the industry’s default embedded database, now officially designated as a Recommended Storage Format (RSF) by the U.S. Library of Congress (Source: loc.gov RFS 2026). It remains the most depl
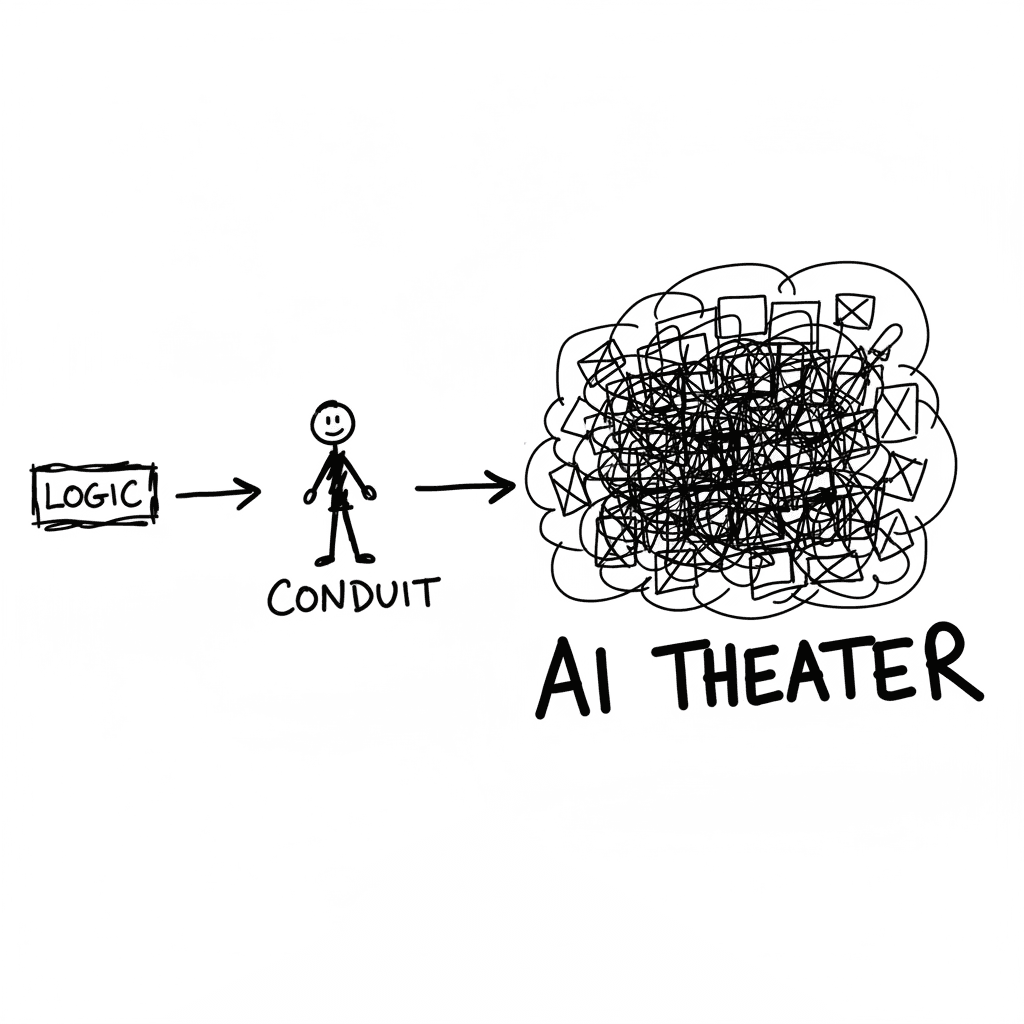
The Conduit Problem: Generative AI and the Hollowing of Technical Expertise
The primary metric for developer productivity in mid-2026 has shifted from logic density to artifact volume, fueled by LLM-driven "elongation" of workplace outputs. This phenomenon, labeled AI Product
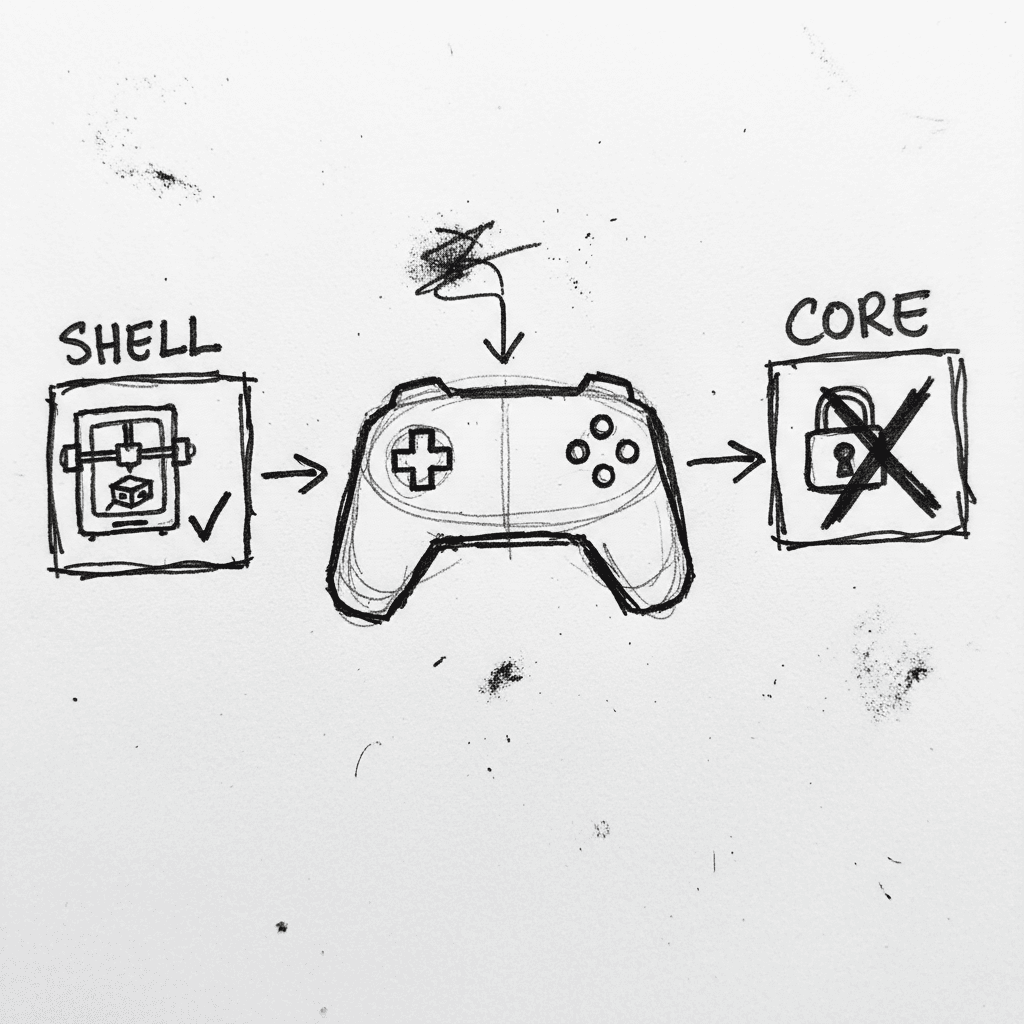
Valve Releases CAD Files for Steam Controller 2026 and Magnetic Puck
Valve has published the full engineering specifications and CAD files for the 2026 Steam Controller shell and its magnetic charging "Puck" on GitLab. (GitLab) This release, licensed under CC BY-NC-SA
Stay Ahead of AI Adoption Trends
Get our latest reports and insights delivered to your inbox. No spam, just data.