The Linux Kernel ‘Copy Fail’ and the Argument for Software Abstinence
CVE-2026-31431 is a deterministic Linux kernel Local Privilege Escalation (LPE) affecting nearly every major distribution released since 2017 (Source: Palo Alto Networks). Infrastructure authority Xe

The Pitch
CVE-2026-31431 is a deterministic Linux kernel Local Privilege Escalation (LPE) affecting nearly every major distribution released since 2017 (Source: Palo Alto Networks). Infrastructure authority Xe Iaso argues that the current surge in AI-orchestrated supply chain attacks makes installing any new software a net-negative for security. The thesis suggests that until the "Copy Fail" logic flaw is fully mitigated, the only winning move is to stop adding dependencies.
Under the Hood
The "Copy Fail" vulnerability is a catastrophic logic flaw discovered through AI-assisted fuzzing in April 2026. It allows an attacker to write four controlled bytes into the page cache of any readable file, which effectively enables the corruption of su or sudo binaries in memory (Source: Cloudflare Blog). This bypasses traditional on-disk integrity checks, as the corruption exists only in the volatile page cache.
Active exploitation is currently leveraging compromised NPM packages, such as the recent ua-parser-js incident, to gain an initial foothold before using Copy Fail to reach root (Source: El Ecosistema Startup). CISA has already added the flaw to its Known Exploited Vulnerabilities catalog, setting a strict remediation deadline of May 15, 2026 (Source: CISA/NHS Digital).
The architectural risk is highest in multi-tenant environments. Microsoft has confirmed that Copy Fail allows for consistent escapes from Kubernetes containers into the underlying host environment (Source: Microsoft Security Blog). The threat is compounded by supply chain bloat; even a "minimal" utility like 7-Zip now carries over 300 unique dependencies, each representing a potential entry point for the LPE (Source: SANS Institute 2026).
We do not know yet if the "Software Abstinence" movement has significantly slowed developer velocity in Q2 2026. Additionally, there is no public list of SaaS providers that have successfully mitigated the algif_aead module—the root of the flaw—without breaking production cryptographic features.
Marcus's Take
Xe Iaso is right to be paranoid, even if "total abstinence" sounds like a sysadmin's fever dream from 1996. In an era where generative AI and AI-assisted fuzzing can surface logic flaws faster than human maintainers can ship patches, your CI/CD pipeline is a loaded gun pointed at your production cluster. If a dependency isn't mission-critical, it has no business being in your environment until the May 15 deadline has passed and the dust settles. Stop decorating your stack and start pruning it.
Ship clean code,
Marcus.

Marcus Webb - Senior Backend Analyst at UsedBy.ai
Related Articles
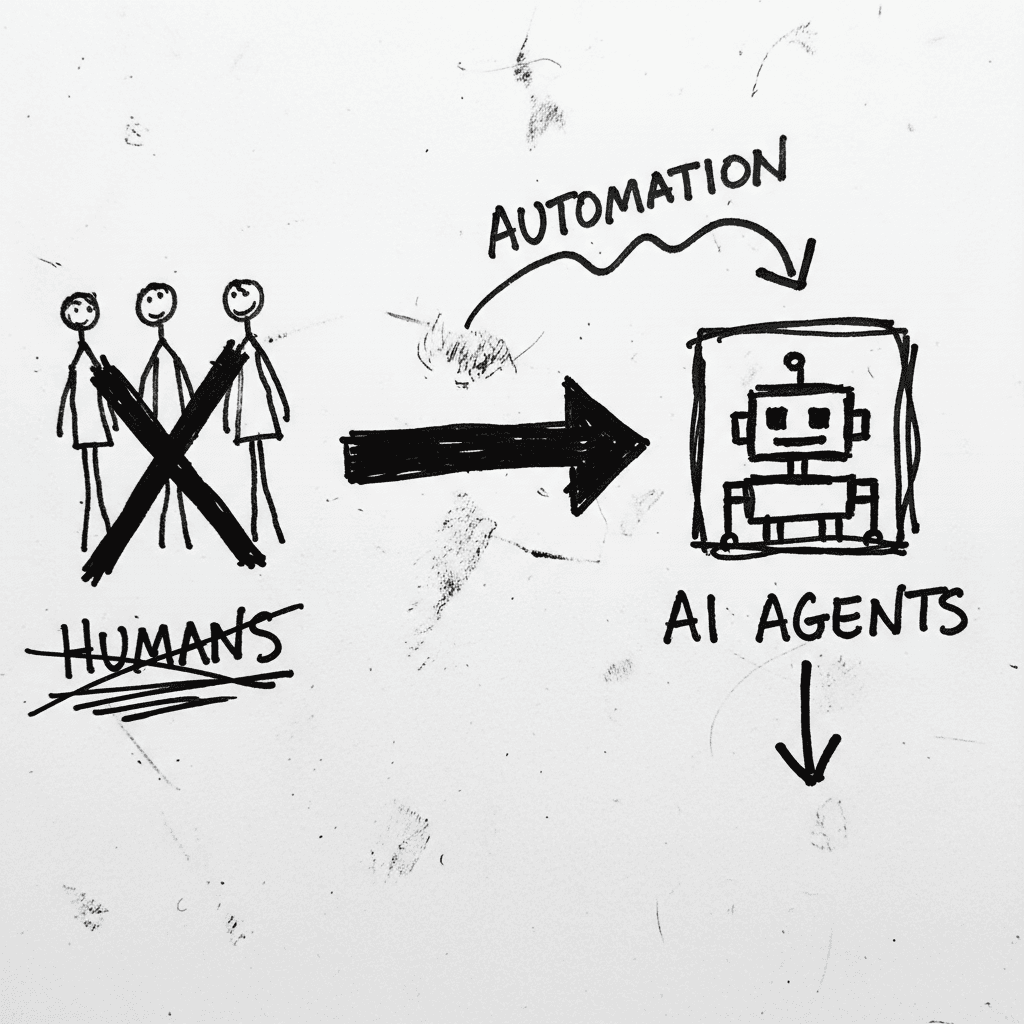
Cloudflare’s Agentic Restructuring and the 20% Workforce Cut
Cloudflare has announced a 20% reduction in its global workforce, citing a pivot to "agentic AI" as the primary driver for operational efficiency. While management claims internal AI agent usage incre
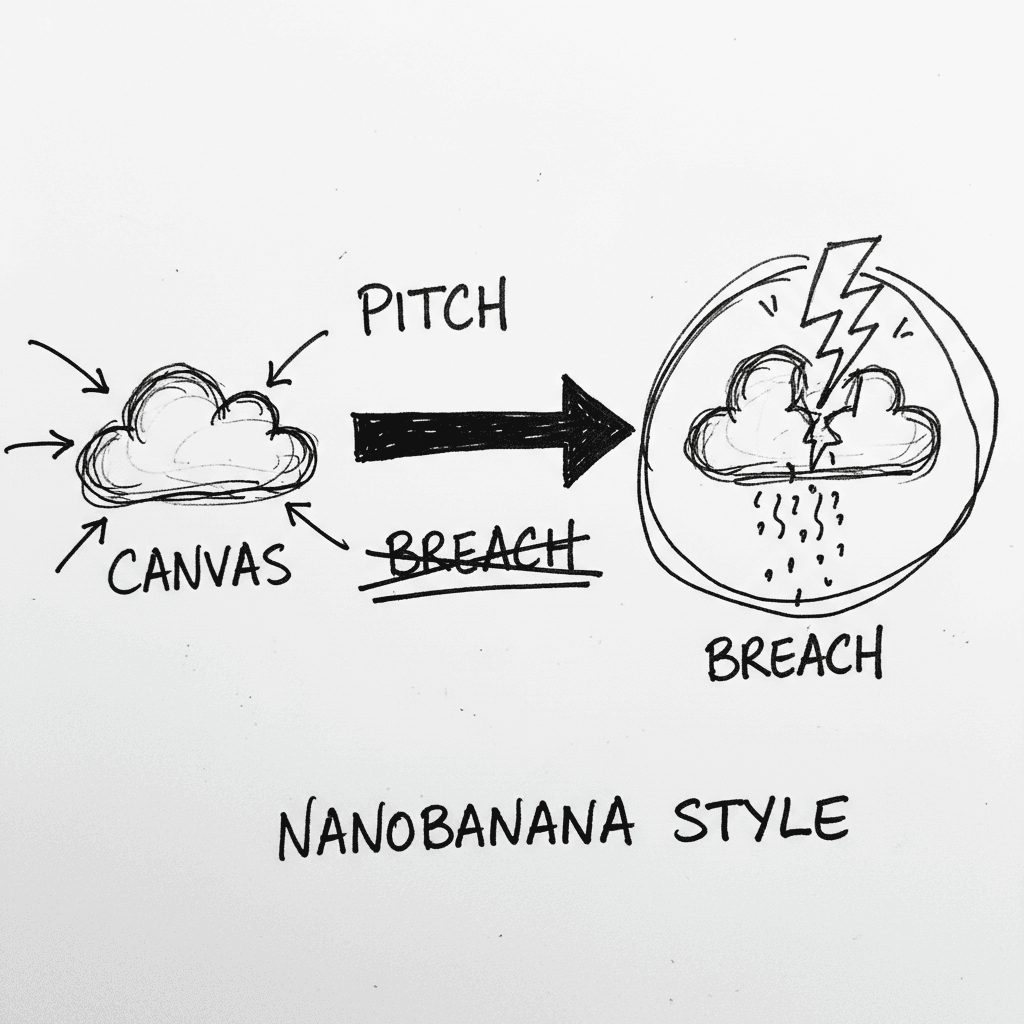
Instructure’s Canvas LMS crippled by nationwide outage and data breach during finals week
Canvas is the dominant Learning Management System (LMS) used by major institutions to centralize curriculum and satisfy ADA accessibility requirements. It is currently the focus of intense scrutiny as
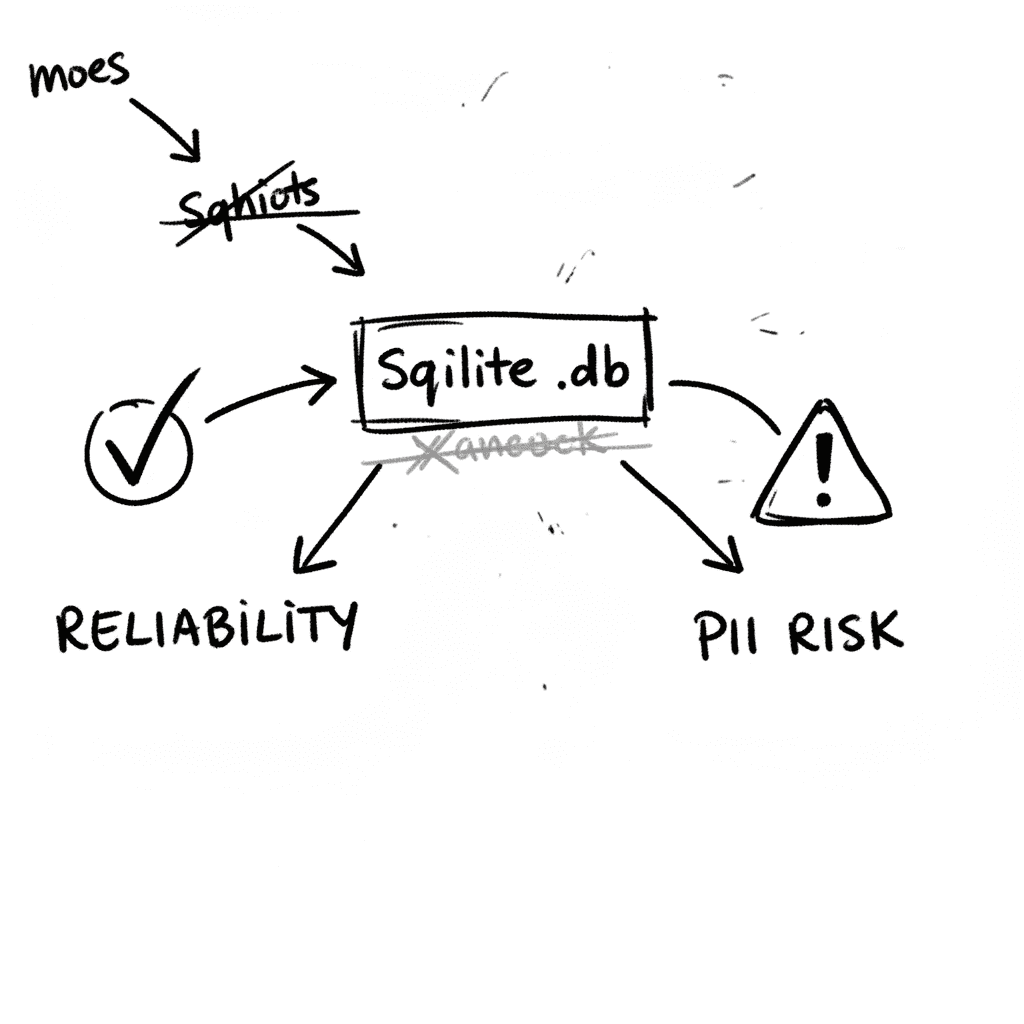
SQLite 3.53.1: Technical Reliability vs. Compliance Governance
SQLite is the industry’s default embedded database, now officially designated as a Recommended Storage Format (RSF) by the U.S. Library of Congress (Source: loc.gov RFS 2026). It remains the most depl
Stay Ahead of AI Adoption Trends
Get our latest reports and insights delivered to your inbox. No spam, just data.