The Security Regression of Modern Windows Notepad
Microsoft has transitioned the Store-based Notepad from a basic system utility to a "reimagined" productivity tool featuring Markdown support and AI-assisted editing (Source: Microsoft Store). This sh

The Pitch
Microsoft has transitioned the Store-based Notepad from a basic system utility to a "reimagined" productivity tool featuring Markdown support and AI-assisted editing (Source: Microsoft Store). This shift from a simple text editor to a rich application has fundamentally compromised its decades-old security profile. Hacker News is currently dissecting how a tool meant for "dumb" text now handles complex command execution.
Under the Hood
The central technical fact is CVE-2026-20841, a high-severity Remote Code Execution (RCE) vulnerability with a CVSS score of 8.8 (Source: CVE.org, Feb 2026). This flaw is a direct result of improper command injection (CWE-77) within the Markdown link handling logic of build 11.2510 and later (Source: CybersecurityNews.com).
Exploitation occurs when a user clicks a malicious link inside a Markdown (.md) file, which triggers unverified protocols to fetch and run remote payloads (Source: Talos Intelligence). This effectively allows an attacker to execute arbitrary commands with the privileges of the logged-in user. While the modern UWP/Store version is compromised, the legacy Win32 Notepad.exe remains unaffected (Source: Hacker News).
The integration of these rich-text features has created a massive and unnecessary attack surface in a utility users historically perceived as "safe" (UsedBy Dossier). We don't know yet if Microsoft will implement a "Restricted Mode" to disable link-handling in system utilities. Furthermore, it is currently unclear if the AI-integration (Copilot/Recall) in the 2026 Windows builds interacts directly with this vulnerable Markdown parser.
Marcus's Take
Notepad’s only utility was its predictability; it was the one place you could paste a string without worrying about the underlying parser losing its mind. By grafting a Markdown engine onto a system binary, Microsoft has turned a low-risk tool into a high-value phishing vector. It is a classic case of feature bloat masquerading as progress. Delete the Store version, revert to the legacy binary, and keep your Markdown work inside a proper, sandboxed environment like VS Code.
Ship clean code,
Marcus.

Marcus Webb - Senior Backend Analyst at UsedBy.ai
Related Articles
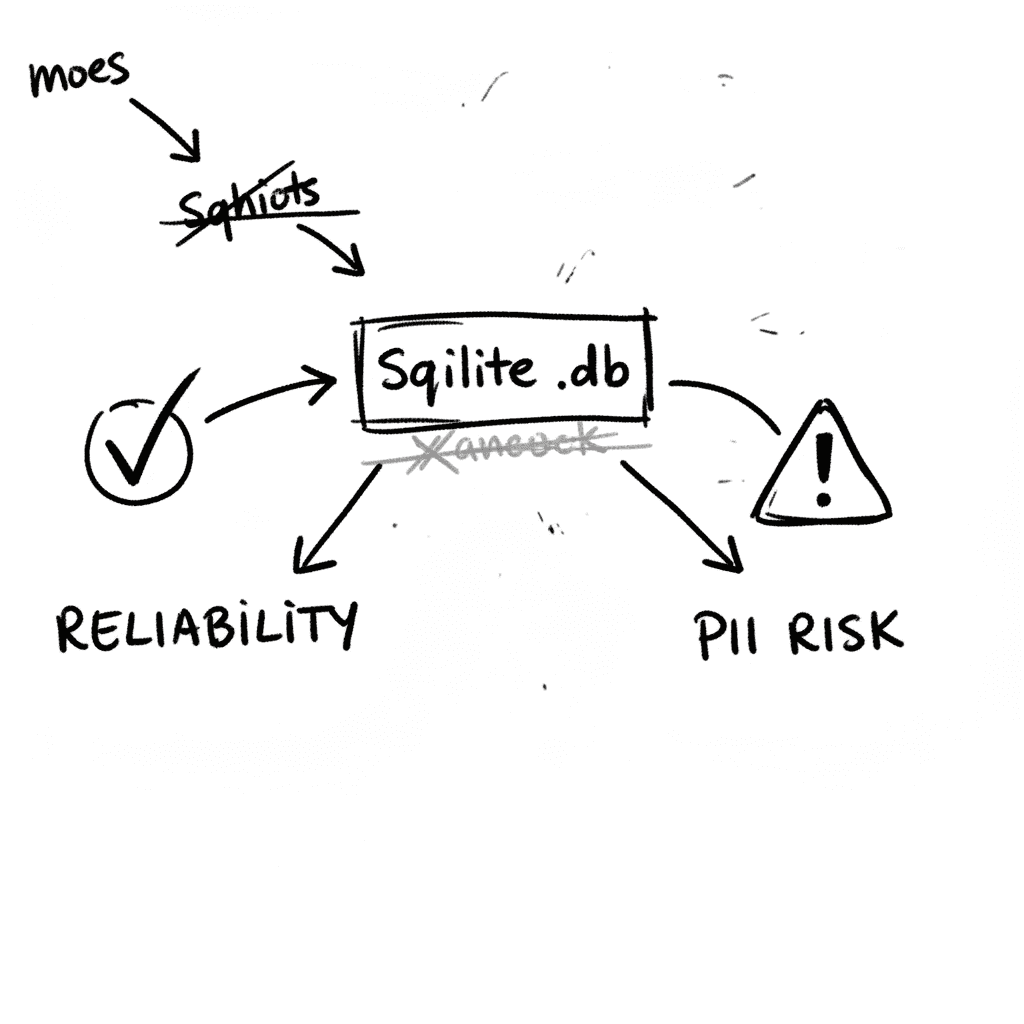
SQLite 3.53.1: Technical Reliability vs. Compliance Governance
SQLite is the industry’s default embedded database, now officially designated as a Recommended Storage Format (RSF) by the U.S. Library of Congress (Source: loc.gov RFS 2026). It remains the most depl
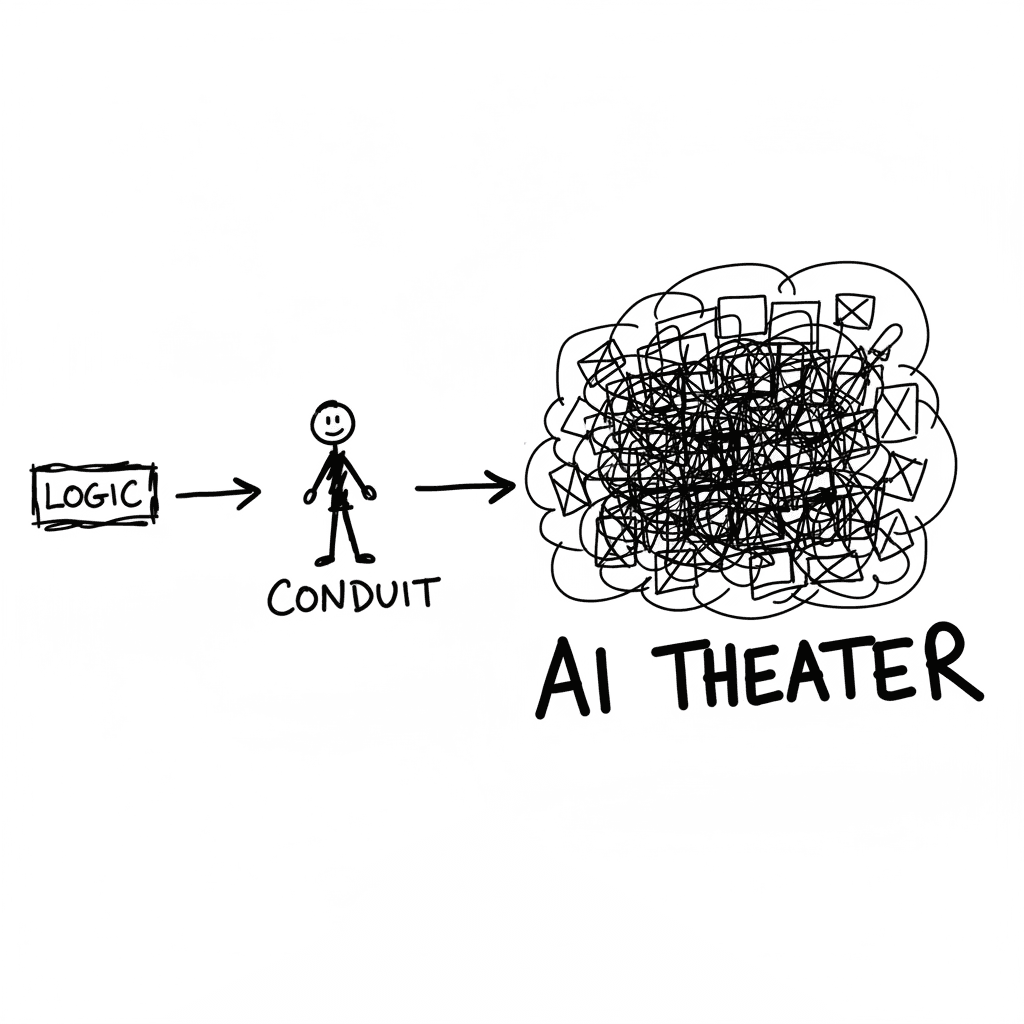
The Conduit Problem: Generative AI and the Hollowing of Technical Expertise
The primary metric for developer productivity in mid-2026 has shifted from logic density to artifact volume, fueled by LLM-driven "elongation" of workplace outputs. This phenomenon, labeled AI Product
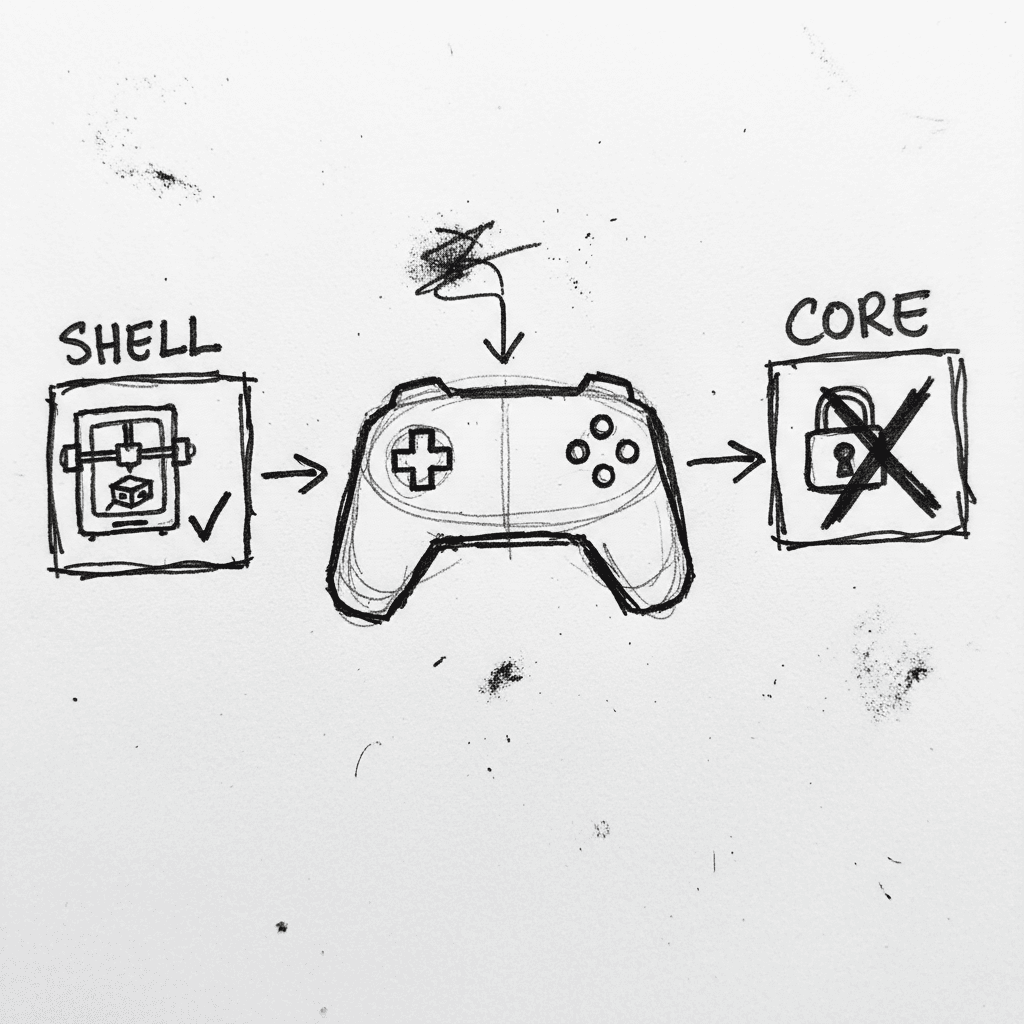
Valve Releases CAD Files for Steam Controller 2026 and Magnetic Puck
Valve has published the full engineering specifications and CAD files for the 2026 Steam Controller shell and its magnetic charging "Puck" on GitLab. (GitLab) This release, licensed under CC BY-NC-SA
Stay Ahead of AI Adoption Trends
Get our latest reports and insights delivered to your inbox. No spam, just data.