Security Analysis: Vercel Infrastructure and the April 2026 Supply Chain Breach
Vercel confirmed a significant security breach on 19 April 2026, originating from a third-party AI supply chain attack (The Register). The entry point was Context.ai, an AI tool that obtained an "Allo

The Pitch
Vercel is the deployment platform for the Next.js ecosystem, prioritising developer experience and edge delivery for modern frontend frameworks. It currently manages deployments for 312 companies in the UsedBy database, including enterprise teams at Loom and HashiCorp. See Vercel profile
Under the Hood
Vercel confirmed a significant security breach on 19 April 2026, originating from a third-party AI supply chain attack (The Register). The entry point was Context.ai, an AI tool that obtained an "Allow All" Google Workspace OAuth token from a Vercel employee (Source: Context.ai Security Update). This lateral movement allowed attackers to access Vercel's internal environments.
Exposure was restricted to internal systems and customer environment variables not explicitly marked as "sensitive". While sensitive-flagged variables remained encrypted, older configurations and certain Neon database integrations pre-dating February 2024 often default to cleartext visibility via internal APIs (Sources: Vercel Security Bulletin, GitGuardian). This reveals a systemic "concentration of trust" risk within the platform.
This incident follows two critical vulnerabilities disclosed within the last 14 months. React2Shell (CVE-2025-55182), a Remote Code Execution vulnerability in React Server Components with a CVSS of 10.0, was patched in December 2025 (Source: Rapid7). Additionally, a Middleware Bypass vulnerability (CVE-2025-29927) with a CVSS of 9.1 affected Next.js applications in March 2025 (Source: GitHub).
We don't know yet the final count of affected customers, though official statements currently mention a "limited subset" (Source: Vercel). We also cannot verify claims by the threat actor group ShinyHunters regarding the alleged $2 million sale of exfiltrated data. The reliance on centralized defaults, often reinforced by automated agents like Claude Code, has created a massive blast radius for single-vendor failures (Source: Amplifying.ai Report).
Marcus's Take
Vercel’s obsession with frictionless developer experience has finally hit the wall of infrastructure reality. While the React2Shell patch was handled professionally, the Context.ai breach proves that internal human error and unvetted AI "office suites" are now the primary threat vector for your deployment pipeline. If you are running mission-critical workloads on Vercel, move your secrets to a dedicated vault like AWS Secrets Manager or HashiCorp Vault immediately. Do not rely on native environment variable management for production credentials.
Ship clean code,
Marcus.

Marcus Webb - Senior Backend Analyst at UsedBy.ai
Related Articles
Technical Analysis of OpenAI gpt-image-2 Rendering Engine
OpenAI launched ChatGPT Images 2.0 (gpt-image-2) on April 21, replacing the gpt-image-1.5 model with a focus on reasoning-driven spatial layouts. The system shifts away from simple pixel prediction to
The Atomic Semi Technical Assessment: Portable Silicon Fabrication in 2026
Atomic Semi is a venture-backed startup co-founded by Sam Zeloof and industry veteran Jim Keller that aims to decentralise semiconductor manufacturing. By building small, portable "mini-fabs," the com
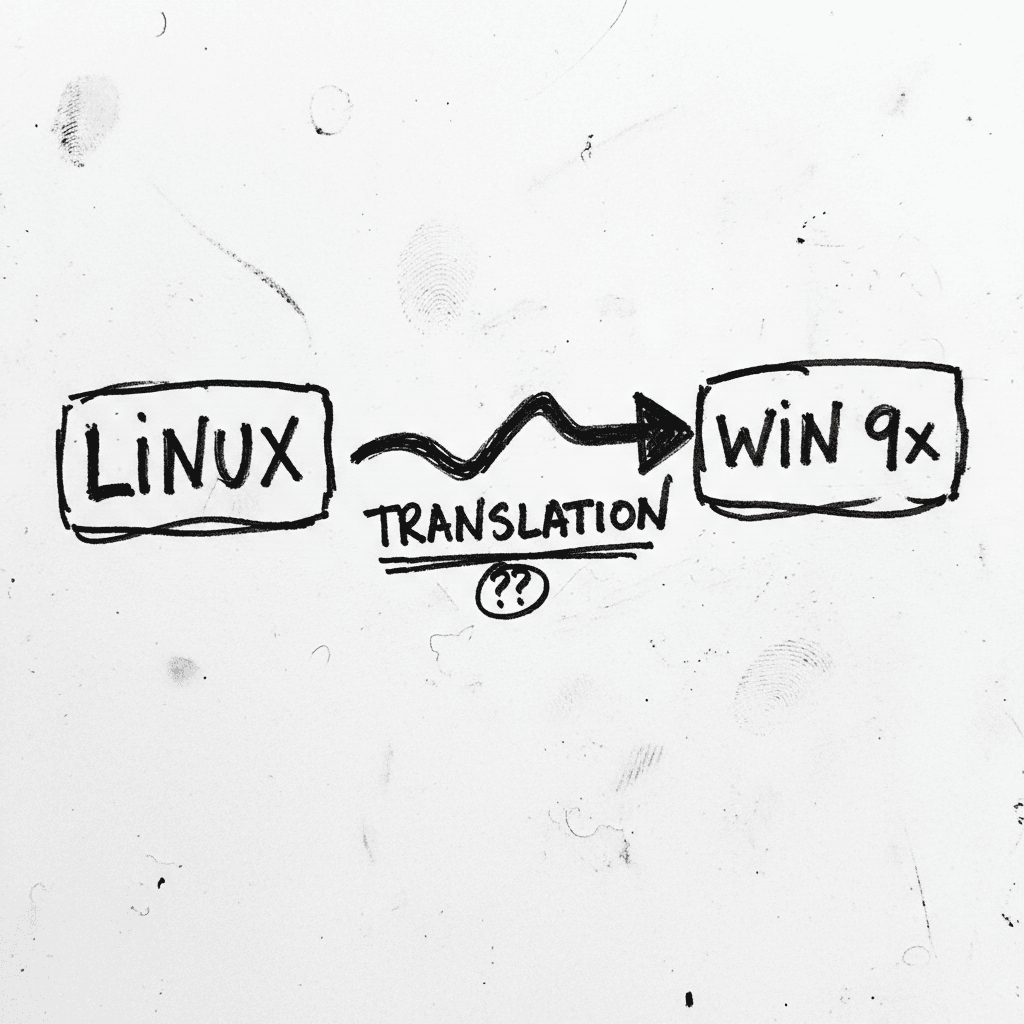
W9SL: Syscall Translation for Legacy Windows 9x Kernels
Windows 9x Subsystem for Linux (W9SL) is a syscall translation layer that allows unmodified Linux ELF binaries to run on Windows 95, 98, and Me without virtualization. It mimics the architecture of th
Stay Ahead of AI Adoption Trends
Get our latest reports and insights delivered to your inbox. No spam, just data.